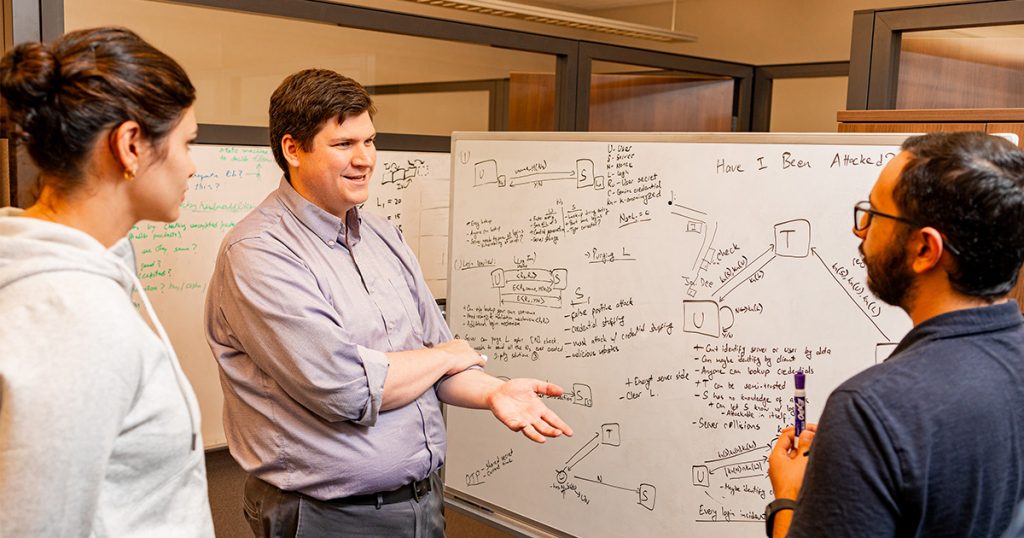
Scott Ruoti, an assistant professor in the Min H. Kao Department of Electrical Engineering and Computer Science, is establishing the groundwork for developing systems that help individuals manage their online security.
Ruoti has received a National Science Foundation Faculty Early Career Development (CAREER) Program award of $654,235 over five years for research on the management of cryptographic keys.
In the simplest terms, a cryptographic key is a large random number, tens to thousands of digits long.
“Cryptographic keys are a vital part of any security system,” Ruoti explained. “They do everything from data encryption to user authentication.”
As long as the cryptographic keys used by a security system remain secret, that system is secure.
While cryptographic keys play a role in many computer transactions, from sending emails and visiting websites to making online purchases and managing cryptocurrency, most key management is done behind the scenes. The average person is unaware that it is happening, much less how it works. For example, emails automatically undergo encryption and decryption as they are transmitted between email services such as gmail.com or utk.edu.
Security researchers have begun proposing exciting new systems that require users to be aware of their cryptographic keys. For example, cryptocurrency—currency that exists only in digital form―is stored in a digital wallet and exchanged through the use of cryptographic keys. Similarly, self-sovereign data software automatically encrypts documents uploaded to a cloud storage system so only the user can see it. Others—including the cloud storage provider—can’t view it without the appropriate cryptographic key.
“The future is going to see the creation of ever more advanced cryptosystems, so we’ve got to figure out how to help people manage their cryptographic keys,” Ruoti said. “The compromise of any cryptographic key could lead to the collapse of an organization’s entire security infrastructure, allowing the attacker to decrypt sensitive data, authenticate themselves as privileged users, or give themselves access to other sources of classified information.”
But using cryptographic keys is complex. Devising software that allows individuals to understand and use cryptographic keys, and to recover lost keys, is growing in importance as technology evolves.
Key management is a difficult issue that has remained unsolved for about 30 years, Ruoti said. While it may take decades to come up with a form of effective key management easy enough for general use, he believes his project will establish a foundation.
He’ll start by studying communities, primarily computer system developers, that have been successfully using cryptographic keys. He’ll look at software systems and other existing tools that help people manage cryptographic keys to see what works. And he’ll observe test groups using cryptographic keys over a lengthy period to see where they encounter problems and make mistakes.
“This research is creative and original in that it breaks from the status quo of studying key management within a single application domain and use case, and instead studies it across many application domains and use cases to identify generalizable principles and practices,” he said.
As required by the CAREER award program, Ruoti’s project includes components that support precollege and undergraduate education and public education about the work.
“My central hypothesis is that many students—particularly traditionally marginalized students—are more likely to pursue further computer science and computer security education if they experience how it involves more than just software engineering,” he said.
Ruoti is also working with UT Institute of Agriculture’s Lone Oaks Farm to develop experiential curricula on computer security for K–12 students.
Contact
Amy Blakely ((865-974-5034, ablakely@utk.edu)